Advancing technology can strengthen healthcare cybersecurity capabilities, improving organizational protections of patients’ digital data. Yet those same advancements have enabled more sophisticated malware and breach techniques, intensifying the need for robust security protocols. This is especially true as data breaches continue to rise, risking protected health information (PHI) exposures for millions of patients annually.
As the cyber threat landscape evolves, healthcare facilities must employ a comprehensive digital security framework that extends beyond software alone. A balanced approach that integrates the latest technology, well-defined processes, and adequately trained personnel is necessary.
In this guide, we’ll explore why strong cybersecurity defenses are crucial and alert you to several red flags that may indicate systemic vulnerabilities. We’ll also introduce some best practices for strengthening your cyber safety net and help you to build a resilient, multilayered defensive framework that protects both patients’ data and your organizational reputation.
What Makes Healthcare Cybersecurity Uniquely Vulnerable?
Health data offers an attractive target because it contains reliable and permanent personal information. Beyond that, modern healthcare delivery relies on highly connected systems that integrate physical operational devices with digital networks (like patient monitoring through telemetry). This level of connectivity can enable streamlined operational flow and efficient, real-time communication across care teams. However, it also expands the potential for cyberattacks.
Integrated health processes and systems present multiple digital access points that can be exploited without proper protections. The consequences of a cyberattack in clinical settings, unlike in other fields, often extend well beyond financial or operational loss. For example, if hackers were to disrupt the functionality of critical patient devices (like a ventilator), it would jeopardize patients’ lives and wellbeing. No matter the level of clinical interference, each cyber incident risks eroding patient trust, compromising care plan engagement and patient-provider relationships.
Healthcare Red Flags for Insufficient Cyber Defenses
The long-term consequences of cyberattack incidents underscore the importance of cybersecurity in healthcare and demonstrate why organizations must secure access to PHI and data networks. Beyond an overt cyberattack, these red flags can signal increased vulnerability or a potential breach:
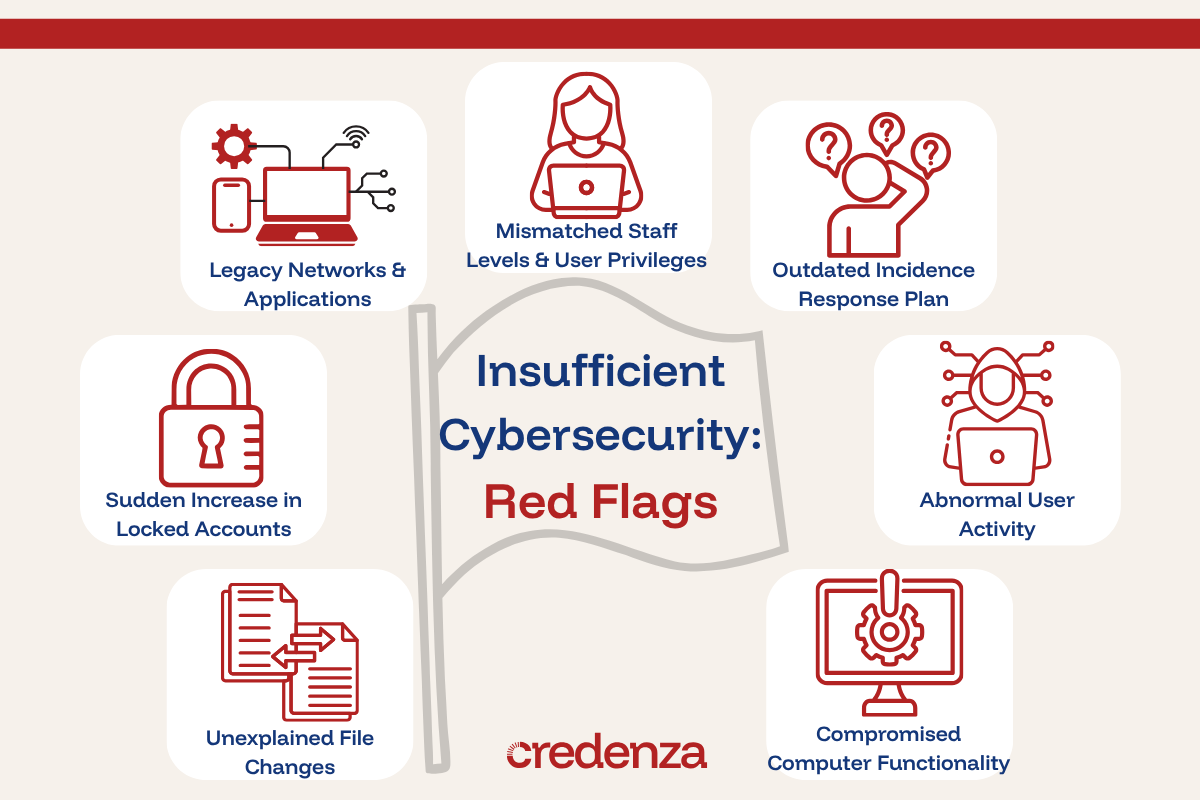
Legacy Networks and Applications
Outdated systems weren’t built to keep up with today’s artificial intelligence (AI)-driven malware and scams. Even if the system has transferred to a modern defensive software platform, many healthcare facilities still maintain old servers, kept for specific medical devices or services. These historical systems offer easy targets for innovative cyberattack strategies.
Mismatched Staff Levels and User Privileges
Healthcare facilities can require large workforces to meet patient demand. Hiring bursts and frequent turnover can complicate access management and monitoring. When the number of active accounts exceeds current staffing levels, those unused access points can become overlooked vulnerabilities, creating potential entry points for unauthorized access.
An Outdated Incident Response Plan
Downtime processes and cyber incident response plans should be living documents that are updated according to emerging threats and shifting clinical priorities. If a facility’s response lays forgotten within a dusty emergency binder, cybersecurity isn’t being taken seriously; this makes the entire system vulnerable to the full spectrum of consequences should a breach occur.
Sudden Increase in Locked Accounts
One healthcare staff member getting locked out of their account (perhaps due to a forgotten password) isn’t worth investigating. However, when a large number of accounts lock in quick succession, that could signal intrusion efforts. Any significant increase in locked user accounts warrants cybersecurity follow-up.
Abnormal User Activity
Workflow within clinical spaces often becomes habitual for most employees. This means that their computer activities largely follow the same patterns each day. Disruptions to those patterns can indicate trouble. Examples include a surge of logins across multiple unknown devices, large-scale unplanned password changes, and user activity that falls outside of normal working hours
Unexplained File Changes
File modifications that don’t correspond with clinical or administrative workflows are another warning sign. Unexplained changes that look suspicious should be reported to healthcare cybersecurity teams in case they indicate unauthorized access and attempts to insert malware or copy (and steal) data.
Compromised Computer Functionality
Healthcare environments are often fast-paced. So, when a computer glitches or load times suddenly increase, clinicians and other team members typically notice right away. Rather than simply being annoying, these minor disruptions can indicate a larger issue. Frequent website redirects, prolonged loading timeframes, and glitchy interfacing are often warning signs of a cybersecurity incident.
The Relationship of Cybersecurity and Healthcare Outcomes
The connection between patient safety and cybersecurity seems clear when discussing examples like critical infrastructure (such as that disrupted ventilator example). Those one-off events don’t actually portray the full clinical impact of digital security lapses, though.
Healthcare cyberinsecurity can lead to events that exacerbate clinician workloads and interrupt standard workflow and safety measures, contributing to clinical consequences including:
- Delayed necessary treatments, procedures, or tests.
- Increased medical procedure complications.
- Prolonged patient length-of-stays.
- Costly (and risky) patient transfers or diversions to alternate facilities.
- Increased patient mortality rate
Cybersecurity for Healthcare Today: Best Practices
A robust approach to healthcare cybersecurity safeguards patient lives, health, and wellbeing. It also protects organizational wellbeing through long-term cost savings and a well-preserved reputation. Here are five key best practices for making the most of your cybersecurity software and processes.
1. Invest in Healthcare Cybersecurity Technology and Personnel
Think of cybersecurity as a crucial form of risk management. It may require upfront investment, but it protects both your organization and patient safety. Over time, these early investments can save you money by avoiding the costs associated with a security event, especially with real-time assistance from the latest technological innovations. Organizations also benefit from investing in knowledgeable personnel and well-defined processes to ensure that protections are implemented and effectively maintained.
Example:
A small rural hospital realizes that all of its imaging systems rely on outdated servers to transmit diagnostic data to the electronic health record (EHR) system. Recognizing the security risk (and with buy-in from key stakeholders), both the imaging devices and their supporting infrastructure are updated, ensuring the devices’ secure, reliable integration with modern clinical systems.
2. Use a Risk-Based Approach to Cybersecurity in Healthcare
Risk mapping can help facilities identify the processes and assets that are most vulnerable to a cyberattack. This enables organizations to effectively target their cyberdefense approach and protect those critical junctions. Even with heavy investments in comprehensive digital security, resources need to be prioritized. A risk-based approach ensures those allocations align with systemic priorities and objectives.
Example:
A primary care office relies heavily on email communication to manage patient concerns, questions, and follow-up communication. During a risk assessment, compliance and cybersecurity administrators identify these emails as a high-risk area due to the frequency and volume of PHI transmission. With further evaluation, the team prioritizes this risk and partners with a HIPAA-compliant secure messaging platform to ensure comprehensive data safety amid frequent external messaging.
3. Train for Worst-Case Scenario Cyber Incidents
HIPAA compliance and awareness training is only one aspect of a comprehensive cybersecurity staff training program. To avoid many of the negative patient outcomes associated with a cyberattack, staff need to know how to deliver care amid planned and unplanned EHR downtimes. This means assigning clear roles and responsibilities for downtime events (or cyberattack response procedures) that are established well before an actual incident occurs.
Example:
A medical-surgical hospital unit performs quarterly downtime simulation training that requires nursing staff to demonstrate competency with paper charting and practice safely administering medications without electronic safety checks. This facilitates a culture of safety and readiness that optimizes clinical standards even in the face of EHR interruptions.
4. Continuously Monitor for Cyber Threat Landscape Changes
Advancing technologies often drive more sophisticated cyberattacks in addition to better security measures. The constant development of both means that healthcare facility leaders must stay up to date on emerging vulnerabilities, attack methods, and shifting threat targets. Proactive monitoring can help organizations to adapt their defenses before a breach actually occurs.
Example:
An ambulatory surgical center manager learns of a cybersecurity attack on a nearby, large hospital system. Recognizing the relevance of these threats to their facility, they conduct a risk review of their own system and subscribe to trusted cybersecurity alerts to ensure they stay updated on the latest digital health news. They also reinforce this knowledge by subscribing to an expert-vetted digital health podcast for additional cybersecurity insights.
5. Treat Healthcare Cybersecurity Programs as a Year-Round Priority
October may be the National Cybersecurity Awareness Month (NCSAM), but cybersecurity in healthcare requires consistent, year-round attention. Encourage vigilance through regular staff updates, targeted training opportunities, and ongoing communication efforts. Promoting professional development (like cybersecurity in healthcare certifications among staff) can further strengthen internal engagement and expertise, facilitating a culture of security awareness.
Example:
A hospital incentivizes members of its compliance and cybersecurity teams to become certified in Healthcare Privacy and Security (CHPS). These staff members are then better positioned to serve as subject matter experts, leading training sessions and supporting frontline staff. This improves organization-wide awareness and strengthens overall cybersecurity practices.
Need Strategies for Engaging Staff in Safeguarding PHI?
Healthcare cybersecurity often starts with awareness and grows in a safety-first culture. Champion this type of engagement with the help of our expert-backed facility guides and management insights, all designed to support patient and organizational outcomes.
